Join 40,000+ sales and marketing pros who receive our weekly newsletter.
Get the most relevant, actionable digital sales and marketing insights you need to make smarter decisions faster... all in under five minutes.
Last year, IMPACT reported on a new analytics tool that would allow marketers to get a peek behind the curtain of their competitors’ performance — Nacho Analytics.
Yes, named after the popular dad joke…
And just like the dad joke suggests, Nacho Analytics aimed to provide you data that was not yours (get it?).
However, Nacho Analytics did more than simply offer basic insights. The tool displayed data as if you were looking right into your competitors' Google Analytics platform, showing virtually the same in-depth insights as you’d get on your own account.
Since you’re only as strong as your competition in the digital marketing space, the ability to view how other companies in your industry are doing is certainly attractive to marketers.
Still, one major question remained: "Is this even legal?"
Reps from Nacho Analytics assured customers that, while the tool is intended to look like you’re essentially hacking your competitors’ Google Analytics account, the service is 100% legal, stating:
“Yes, it’s 100 percent legal and completely complies with Google’s terms of service. We aren’t actually hacking Google or anyone’s Google analytics account, though it might seem that way. Instead we are gathering data from millions of opt-in users, individuals from around the world that agreed to share their browsing data anonymously. Nacho Analytics scrubs this data so all personal information is deleted and so it’s GDPR compliant. This type of data gathering is far from a new innovation. On the contrary, it’s kind of how the Internet runs.”
However, on July 9th, not even a year after the tool was announced, Nacho Analytics tweeted out that an issue with its third-party data provider resulted in a permanent data outage for the service.
Our data partner has ended operations. We apologize for the inconvenience as we halt new sales. We have reached out to our customers about their existing sites, but are also available on live chat or email for assistance. Thanks to everyone for your past enthusiasm and support.
— Nacho Analytics (@NachoAnalytics) July 9, 2019
At first, Nacho Analytics simply was just not selling any more accounts, and customers that chose to keep accounts open would still be able to access any historical data, but no new competitor data or insights.
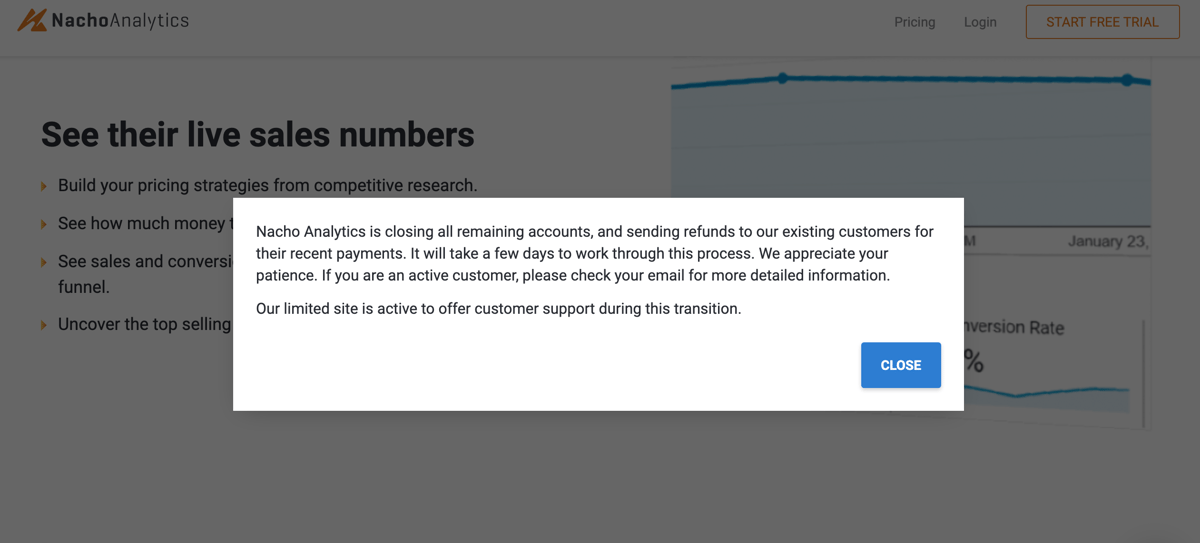
Fast forward to today — if you visit Nacho Analytics’ website, you will see this message:
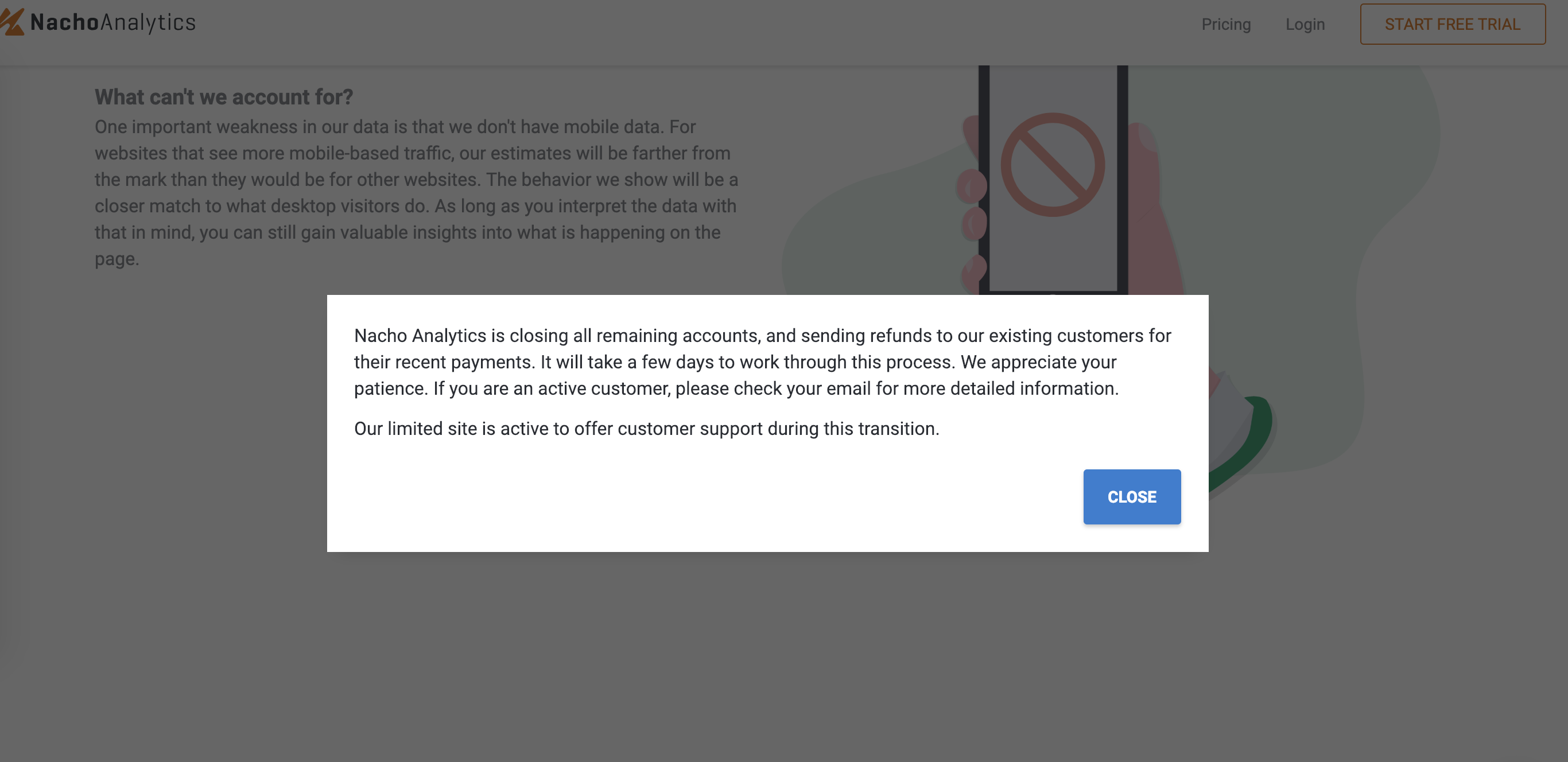
Clearly, this left users with a lot of questions.
Well, after spending way too much time reading up on Nacho Analytics and its history of data collection practices, I have some answers for you.
The fall of Nacho Analytics teaches several important lessons to site owners (and internet users in general) on safe website security practices, and knowing what you’re really signing up for when you accept cookie tracking services.
The fall of Nacho Analytics
To understand why Nacho Analytics shut down, it’s important to understand how it was collecting competitor data.
It’s true that the tool was not hacking competitors' Google Analytics accounts — instead, it was tracking millions of people’s browsing histories to see what pages they were visiting. If they visited your competitor, the metric was added to your Nacho Analytics portal.
To be clear, this method was not a secret by any means — Nacho Analytics makes this clear on its website, stating:
“Millions and millions of people all over the world have opted-in to anonymously share their web browsing history with us. We take that data and load it into a Google Analytics account for you. Anonymous user tracking is how the Internet works — it's just normally the exclusive privilege of billion dollar companies. We're putting that power in your hands.”
While it’s not confirmed exactly how Nacho Analytics was getting these users to opt into data collection, researcher Sam Jadali believes it comes from several different browser extensions that note in their terms of service that they may share user data with third-parties.
At this point, you may be asking yourself: So, what’s the problem with this? Isn’t this how all cookie tracking works?
Well, yes and no.
The issue with Nacho Analytics is that the tool showed third-parties all URLs users visited — and a subset of those URLs led to non-password-protected pages a regular user browsing the internet wouldn’t be able to find.
(Think: things like order confirmation pages, private PDF attachments, and other pages intended for that specific user’s eyes that sometimes aren’t protected by a login screen, but instead, are “blocked” by a set of “tokens” or a series of characters that would be difficult to guess.)
Since Nacho Analytics captured and published these pages, users could go directly to the page and sometimes even view the information on it.
Ars Technica reports that the publication of these URLs has lead to the unintentional sharing of sensitive data, including:
- Home and business surveillance videos hosted on Nest or other security platforms
- Information on recently purchased vehicles, including the vehicle identification number, and the name and address of the buyer
- Sensitive documents posted on Microsoft OneDrive and other cloud-based business platforms, like tax returns, business documents, billing invoices, and presentation slides
- Patient names, doctors they visited, and other details surrounding their appointment when booked on DrChrono, a cloud-based patient care platform
- Travel itineraries placed on Priceline, Booking.com, and other airline services.
Yikes.
Even in cases where the page was password-protected, sometimes the URL and page title gave away enough information to give context into private data that shouldn’t fall into the hands of a user trying to understand their competitors' monthly traffic score.
Here’s a recap Dan Goodin of Ars Technica gave of these examples. I highly encourage you to check out his full article here or Sam Jadali’s in-depth research report to learn more about the scope of the companies affected.
- URLs referencing teslamotors.com subdomains that aren’t reachable by the outside Internet.... Sometimes, the URLs or page titles included vehicle identification numbers of specific cars that were experiencing issues—or they discussed Tesla products or features that had not yet been made public.
- Internal URLs for pharmaceutical companies Amgen, Merck, Pfizer, and Roche; health providers AthenaHealth and Epic Systems; and security companies FireEye, Symantec, Palo Alto Networks, and Trend Micro.
- URLs for JIRA, a project management service provided by Atlassian, that showed Blue Origin, Jeff Bezos’ aerospace manufacturer and sub-orbital spaceflight services company, discussing a competitor and the failure of speed sensors, calibration equipment, and manifolds.
This information is only scarier when you know that this data was available to virtually anyone that signed up for the service.
This was all possible despite Nacho Analytics (and the third-party platforms they collected the data from) promising that all data published to the platform was completely anonymous. Reports showed that some personal identifying information was redacted by the Nacho Analytics team — but in some of those instances, clicking through to the link would lead to the protected data.
Lesson for brands
Many companies make an effort to keep their website hacker-free, but this case presents a big loophole that may have been previously unknown.
First, make sure that you are password-protecting any pages that contain any information that you don’t want accessible by the public.
This includes order confirmations, attachments, or anything else not intended for general visitors else to find.
While that sounds easy enough, it’s also important that anyone who does have password protected pages ensure that URL path and page titles are just as secure. Even if a link expires after a certain amount of time, it can still leave private data vulnerable.
I encourage all brands to take an extra look at their website pixels, employee browser extensions, or anything else that could result in unwanted data sharing.
After all, at the end of the day, nothing Nacho Analytics was doing was necessarily illegal (as far as we know) since all users were opted-in to tracking from one place or another. For this reason, companies need to understand that even though they may not be exploiting user data, their website features may leave users data vulnerable to being placed in the wrong hands.
Free Assessment: